
The Importance of Multi-Factor Authentication in 2025
In today’s digital world, the importance of ensuring the security of online accounts and personal information cannot be overstated. With cyber threats becoming more sophisticated and prevalent, it is crucial for individuals and businesses to take proactive steps to protect themselves. One of the most effective ways to enhance security is through the implementation of […]
Read More
The Rise of Ransomware: How to Stay Protected
Ransomware is a type of malicious software that encrypts a user’s files and demands payment in exchange for decrypting them. It has become a prevalent threat in the tech world, with attacks on businesses and individuals increasing every year. Cybercriminals use ransomware to extort money from their victims, often demanding payment in cryptocurrency to make […]
Read More
How AI is Used in Cybersecurity Defense
In today’s increasingly digital world, cybersecurity is a top priority for businesses and individuals alike. With the rise of cyber threats such as ransomware, phishing attacks, and data breaches, organizations are constantly looking for ways to better protect their sensitive information. One technology that has emerged as a game-changer in the field of cybersecurity is […]
Read More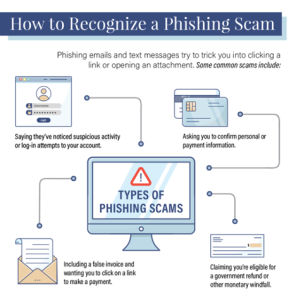
What Is Phishing and How to Protect Yourself?
Phishing is a common online threat that can affect anyone who uses the internet. It involves scammers trying to trick people into revealing sensitive information like usernames, passwords, and credit card details by posing as legitimate organizations or individuals.
Read More
Top 10 VPN Services for Secure Browsing
When it comes to browsing the internet securely and privately, using a reliable VPN service is essential. With the increasing threats to online privacy and security, it’s more important than ever to protect your data from prying eyes. In this article, we’ll explore the top 10 VPN services that offer a combination of security, speed, […]
Read More
The Dark Web: What It Is and Why You Should Care
Have you ever heard of the Dark Web? It’s a mysterious and often misunderstood corner of the internet that has garnered a lot of attention in recent years. But what exactly is the Dark Web, and why should you care about it? In this article, we’ll explore the ins and outs of the Dark Web, […]
Read More
How to Create Stronger Passwords and Avoid Hacking
In today’s digital age, cyber security is more important than ever. With hacking and data breaches becoming increasingly common, it is essential to protect your online accounts with strong passwords. In this article, we will discuss some tips and best practices for creating stronger passwords and avoiding hacking.
Read More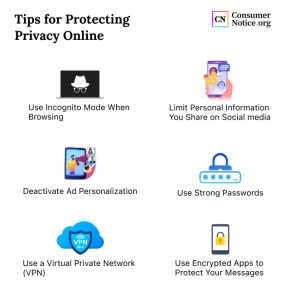
Best Practices for Protecting Your Online Privacy
In today’s digital age, our online privacy is more important than ever. With the increasing amount of personal information we share online, it’s crucial to take steps to protect our data from potential threats. Here are some best practices to help safeguard your online privacy.
Read More
Cybersecurity Trends in 2025: What You Need to Know
With the rapid advancement of technology and the growing interconnectedness of our digital world, cybersecurity has become a top concern for businesses and individuals alike. As we look ahead to 2025, it’s important to stay informed about the latest trends and developments in the cybersecurity landscape to protect ourselves from evolving threats.
Read More
How 5G is Transforming Mobile Technology
With the advent of 5G technology, the mobile industry is on the brink of a revolution. The fifth generation of wireless technology promises to deliver faster speeds, lower latency, and more reliable connections than ever before. This has the potential to completely transform the way we use our smartphones and other mobile devices. In this […]
Read More