Phishing is a common online threat that can affect anyone who uses the internet. It involves scammers trying to trick people into revealing sensitive information like usernames, passwords, and credit card details by posing as legitimate organizations or individuals.
How Does Phishing Work?
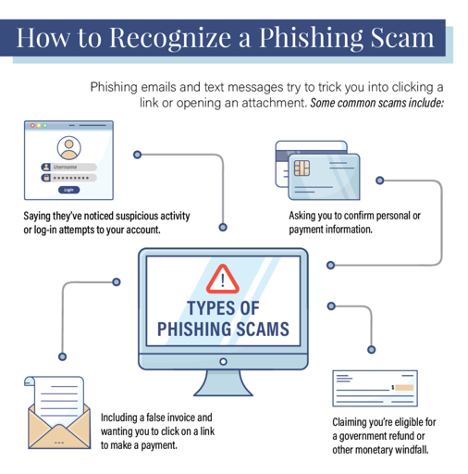
Phishing attacks often come in the form of emails, messages, or websites that appear to be from trusted sources. These messages usually contain urgent requests for personal information or ask the recipient to click on a link that leads to a fake login page designed to steal their credentials.
Types of Phishing Attacks
Email Phishing: The most common type of phishing attack where scammers send fake emails pretending to be from reputable companies.
SMS Phishing: Scammers send text messages that appear to be from legitimate organizations, prompting recipients to click on malicious links.
Pharming: Attackers redirect users to fake websites that resemble legitimate ones to steal their information.
How to Protect Yourself from Phishing
Protecting yourself from phishing attacks requires a combination of vigilance, caution, and the right security tools. Here are some tips to help you stay safe online:
Be Skeptical: Always be cautious of emails or messages asking for personal information, especially if they contain urgent requests or warnings.
Verify the Source: Before clicking on any links or providing sensitive information, verify the sender’s identity and check for any signs of phishing.
Use Security Software: Install reliable antivirus and antimalware software to detect and block phishing attempts on your devices.
Enable Two-Factor Authentication: Add an extra layer of security to your online accounts with two-factor authentication to prevent unauthorized access.
Stay Informed: Keep yourself updated on the latest phishing tactics and educate yourself on how to recognize and avoid potential threats.
Conclusion
Phishing remains a prevalent threat in the tech world, with scammers becoming more sophisticated in their methods. By staying vigilant, verifying sources, and using security tools, you can protect yourself from falling victim to phishing attacks and safeguard your sensitive information online.